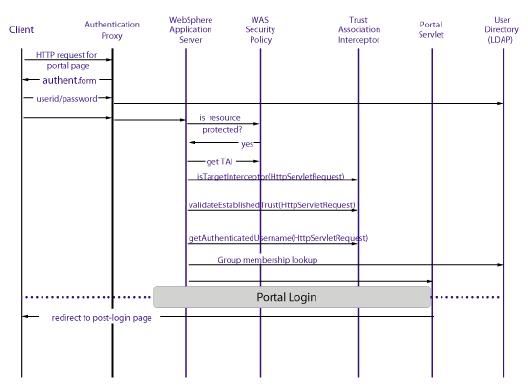
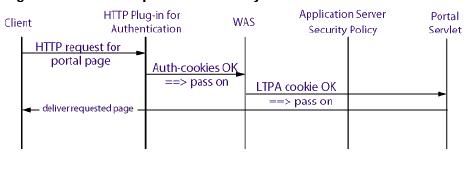
Depending on the type of data that is exchanged between WAS, WPS and your LDPA server you can either configure your LDAP server over SSL or configure it to have direct access to WAS and Portal.
You might want to configure WAS and WPS to access to your LDAP user registry over SSL to ensure that confidentiality of the data exchanged between WAS/WPS and your LDAP. For example user password is sent over the network between LDAP user registry and WPS.This occurs to set the password if WebSphere Portal Express user management tools are used to create users and change passwords and also when WebSphere Application Server authenticates any user name and password pair through an LDAP BIND operation. Configuring LDAP over SSL can be important to protect sensitive data. Also, it might be required to ensure that user attributes that are retrieved from the directory are not viewed by someone watching packets on the network, if the attributes of a user include sensitive information or privacy is a concern.
In general, the task of setting up WebSphere Application Server and WebSphere Portal Express to use LDAP over SSL to the LDAP user registry consists of bringing the necessary certificates into key storage files that WebSphere Application Server and WebSphere Portal Express will use. The necessary certificates mentioned are the signing certificates for the LDAP server certificate. The important point to note is that any certificates required to establish the full certificate signing trust chain must be made available to WebSphere Application Server and WebSphere Portal Express. For a self-signed certificate, the certificate trust chain consists of only the one self-signed LDAP server certificate. For a certificate signed by a CA, the certificate chain confirming the identity and validity of the signing CA must be included. Either a purchased certificate or a self-generated CA signing certificate can be used.Some configuration setting changes must also be made to tell WebSphere Application Server and WebSphere Portal Express that LDAP over SSL should be used. Usually, it is only necessary to bring a signing certificate from the LDAP server to the WebSphere Application Server and WebSphere Portal Express. This step allows the authentication of the server side of the SSL connection. WebSphere Application Server and WebSphere Portal Express are LDAP clients to the LDAP user registry server. The client side is authenticated by doing an LDAP BIND within the SSL connection. The identity used by WebSphere Application Server to perform this BIND is the Bind DN configured on the WebSphere Application Server Security Console. The identity used by WebSphere Portal Express to perform this BIND is the adminId configured in portal_server_root/wmm/wmm.xml.
Steps for setting up LDAP over SSL
It is required that you first get LDAP(non-SSL) successfully working before setting up LDAP over SSL. This allows you to verify that the user registry is responding to LDAP requests before setting it up for SSL.
1. Install WebSphere Portal Express and WebSphere Application Server
2. Install and setup your LDAP
3. Generate or import certificates as necessary and activate SSL on the directory
4. Import certificates to WebSphere Portal Express to enable SSL connection. This process involves exporting the certificate from LDAP server in Base64-encoded ASCII data format as a .arm file. Then on the portal server side you can use ikeyman tool to import the certificate in Java Key Store(.jks ) format. While importing certificate make sure that you import it in .jks file which will be used by WAS server for LDAP over ssl. The WAS server provides a default repertoire called DefaultSSLSetting it contains default WAS trust file which is was_profile_root/etc/DummyServerTrustFile.jks.
5. Perform these steps on WPS. Go to WAS Admin console and check sslEnabled box. You can find it under Security> Global Security > LDAP. Also set LDAP Port to ssl port number.
6. Open portal_server_root/wmm/wmm.xml file in text editor. Navigate to the stanza that begins the ldapRepository name="wmmLDAP". Verify that value of ldapPort attribute is set to ssl port. Next add one more attribute to <ldapRepository> element sslTrustStore="was_profile_root/etc/DummyServerTrustFile.jks". Value of sslTrustStore parameter should be path of java key store format where you imported LDAP certificate.
If you dont specify an sslTrustStore parameter here then member will use app_server_root/java/jre/lib/security/cacerts.jks as trust store and you will have to import LDAP certificate in this file.
7. Restart WPS server.
Take a look at
Step by step instructions for configuring LDAP over SSL document in Infocenter for detailed steps